BUSINESS
V8SQQQ Decoded: Insights for Investors

In the ever-evolving landscape of stock market investments, certain assets capture attention more than others. One such asset is V8SQQQ, a leveraged ETF that has piqued the curiosity of both seasoned investors and newcomers alike. But what exactly does this intriguing ticker represent? As markets fluctuate and investment strategies diversify, understanding V8SQQQ can offer valuable insights for anyone looking to navigate these turbulent waters. This article will peel back the layers on V8SQQQ, exploring its significance in today’s financial world and what it means for your investment portfolio. Whether you’re considering diving in or just want to be informed about new options, there’s plenty to discover here.
Understanding the 3x leveraged ETF
A 3x leveraged ETF amplifies the returns of a specific index by three times. This means if the underlying index rises by 1%, the ETF aims to increase by 3%. Conversely, losses are also magnified.
These products utilize financial derivatives and debt to achieve their targets. They’re designed for short-term trading rather than long-term holds.
Investors often mistake them for traditional ETFs, but they operate under different principles. The daily reset mechanism can lead to performance divergence over time, especially in volatile markets.
Understanding market conditions is crucial when dealing with these funds. Rapid price fluctuations can greatly impact returns, making timing essential.
Risks and benefits associated with investing in V8SQQQ
Investing in V8SQQQ offers unique benefits, particularly for aggressive traders. This 3x leveraged ETF aims to amplify returns on the Nasdaq-100 index. For those who believe in a bullish market trend, this can lead to impressive gains.
However, high rewards come with significant risks. The leverage used means that losses can also be magnified. A sudden downturn could rapidly erode your investment capital.
Moreover, V8SQQQ is designed for short-term trading rather than long-term holding. Daily rebalancing may result in performance drift over time due to compounding effects and market volatility.
Careful monitoring is essential when investing here. Staying informed about market conditions can help you make timely decisions either way—up or down. Understanding these dynamics will empower you as an investor to navigate the complexities of V8SQQQ.
Historical performance of V8SQQQ and its correlation to market trends
The historical performance of V8SQQQ reveals its dynamic nature within the market. This 3x leveraged ETF mirrors the daily movements of the Nasdaq-100 index. As such, it amplifies both gains and losses.
During bullish market conditions, V8SQQQ has shown impressive returns. Investors often flock to it during tech surges, benefiting from rapid price increases in key stocks like Apple and Amazon. It capitalizes on momentum effectively.
However, in bearish phases, volatility strikes hard. The ETF can drop significantly when trends reverse or economic indicators falter. This correlation with broader market shifts highlights its unpredictability.
Analyzing past data suggests that timing is crucial for V8SQQQ investors. Understanding these patterns requires keen observation and a nuanced approach to potential risks involved with high-leverage products in fluctuating markets.
Factors to consider before investing in V8SQQQ
Before diving into V8SQQQ, investors need to assess their risk tolerance. This 3x leveraged ETF amplifies both gains and losses, making it suitable primarily for aggressive traders.
Market conditions play a vital role in the performance of V8SQQQ. A bullish market can enhance returns significantly, while bearish trends can lead to substantial dips.
Investors should also examine their investment horizon. Short-term trading aligns better with leveraged ETFs due to daily recalibration effects that can erode long-term value.
Fees are another aspect worth considering. Higher management fees associated with leveraged ETFs may impact overall profitability over time.
Researching the underlying index is essential as well. Understanding its components will provide insights into potential volatility and price movements linked to V8SQQQ’s performance.
Alternatives to V8SQQQ for investors seeking high-risk, high-reward options
For investors attracted to high-risk, high-reward opportunities, there are several alternatives to consider beyond V8SQQQ.
One option is TQQQ, a popular 3x leveraged ETF that focuses on the Nasdaq-100 Index. It offers similar exposure but tracks different underlying assets.
Another potential choice is UPRO, which provides triple leverage on the S&P 500. This fund can amplify market movements in your favor or against you.
If you prefer sector-specific investments, look into technology-focused ETFs like FNGU. It targets big tech firms and capitalizes on their volatility for potentially higher returns.
Don’t overlook options trading as well; it allows for tailored strategies based on risk appetite while providing significant leverage without traditional equity investment constraints.
Each of these choices carries its own set of risks and requires careful consideration before diving in.
Conclusion: Is V
Investing in V8SQQQ can be an exciting journey. The potential for high returns often draws attention. Yet, it’s essential to stay grounded amid the allure of rapid gains.
This 3x leveraged ETF has its place in a diversified portfolio but requires caution. Market fluctuations can lead to amplified losses as well as profits.
Understanding your risk tolerance is crucial before diving in. Investors need to weigh their strategies and adapt them according to market conditions.
For those considering this investment, ongoing research is vital. Staying informed about trends will help navigate the unpredictable terrain of leveraged ETFs.
Decisions should align with individual goals and financial situations. Patience and diligence could pave the way for success in this dynamic environment.
You Might Like: NoodleMagazine
FAQs
Investing in V8SQQQ can raise many questions. Here are some common inquiries that potential investors might have:
What exactly is V8SQQQ?
V8SQQQ is a 3x leveraged ETF designed to provide three times the daily performance of the Nasdaq-100 index. It’s essential for those looking to amplify their exposure to this tech-heavy market.
How does leverage impact investment returns?
Leverage magnifies both gains and losses. If the underlying index performs well, your returns could be substantial. Conversely, if it declines, your losses will also be significant.
Is V8SQQQ suitable for long-term investing?
Due to its leveraged nature, V8SQQQ is primarily suited for short-term trading strategies rather than long-term holding. It’s important to monitor its performance closely.
What factors should I consider before investing in this ETF?
Consider market conditions, personal risk tolerance, and how comfortable you are with volatility. Understanding these elements can help guide your decision-making process.
Are there alternative investment options similar to V8SQQQ?
Yes, there are other leveraged ETFs available that focus on different indices or sectors. Research various options based on your investment goals and risk appetite.
Can beginners invest in V8SQQQ safely?
While beginners can invest in any asset class they must understand the risks associated with highly leveraged products like V8SQQQ before diving in.
These FAQs highlight key aspects of understanding and navigating investments related to V8SQQQ effectively!
BUSINESS
How Losing Track of Time Can Extend Immigration Detention

In immigration detention cases, time is one of the most important factors—but it’s also one of the easiest to lose track of.
Days turn into weeks, weeks into months, and before long, detention has lasted far longer than expected. This is known as timeline blindness, and it can quietly extend detention without anyone realizing it.
What Is Timeline Blindness?
Timeline blindness happens when individuals and families stop actively tracking how long detention has been ongoing.
This often occurs when:
- The process feels uncertain
- Updates are inconsistent
- There is no clear end date
Without tracking time, it becomes harder to recognize when detention has gone beyond normal expectations.
Why Time Feels Different in Detention Cases
Detention cases don’t always follow a predictable schedule. This can make time feel unclear because:
- There are gaps between updates
- Progress is not always visible
- The case moves in irregular steps
As a result, it becomes difficult to measure how much time has actually passed.
The Risk of Not Tracking Time
When time is not actively monitored:
- Prolonged detention may go unnoticed
- Delays may seem normal
- Opportunities to take action may be missed
What feels like a temporary situation can turn into extended detention without clear awareness.
Why Time Matters Legally
Time is not just a personal concern—it can become a legal issue.
As detention continues:
- Justification must remain strong
- Delays become more significant
- The need for review increases
Without tracking time, it’s harder to recognize when detention may need to be challenged.
Signs Timeline Blindness May Be Happening
You may be losing track of time if:
- You’re unsure how long detention has lasted
- There’s no record of key case events
- Delays feel routine rather than concerning
- There’s no clear timeline for what comes next
These signs indicate that time is no longer being actively monitored.
Rebuilding Awareness of the Timeline
To regain control, it’s important to track:
- The date detention began
- Each hearing or update
- Periods of delay or inactivity
- Changes in case status
This creates a clearer picture of how the case is progressing—or not progressing.
When Time Becomes a Reason to Act
If tracking reveals that detention has continued without meaningful progress, it may be time to take action.
At this stage, working with a Habeas Corpus Lawyer can help bring attention to the length of detention and whether it is still legally justified.
Why Awareness Changes Outcomes
Simply being aware of the timeline can:
- Highlight delays that were previously unnoticed
- Strengthen legal arguments
- Help determine the right moment to act
Awareness turns passive waiting into informed decision-making.
Final Thoughts
Time in immigration detention can easily become blurred, especially when the process feels uncertain. But losing track of time can lead to longer detention without realizing it.
By actively tracking the timeline and recognizing when detention becomes excessive, individuals can take the right steps to move their case forward and avoid unnecessary delays.
BUSINESS
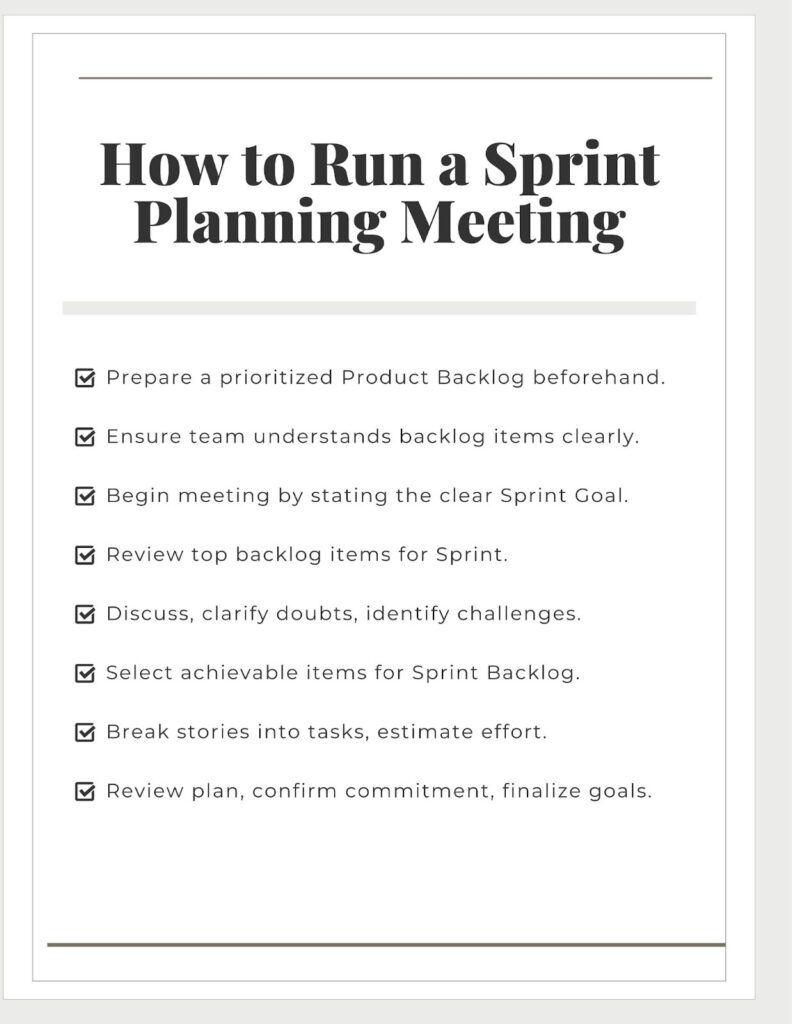
How to Run a Sprint Planning Meeting?

A meeting is a structured conversation between team members with a clear goal in mind. In Agile and Scrum, meetings are inevitable because they create regular opportunities for the team to inspect their work, adapt the discussed plan, and align it with the organization’s goals.
This constant communication and collaboration are an essential part of responding to change and meeting the value delivery. In this article, we discuss how to run a Sprint planning meeting and how it contributes to the Scrum team’s effectiveness.
What is Sprint Planning?
Sprint is a container for all Scrum events (Sprint Planning, Daily Scrums, Sprint Review, and Sprint Retrospective). That means Sprint Planning is also part of the Sprint. Everybody in the team works towards the Sprint Goal.
Sprint Planning is a team meeting at the beginning of every Sprint to answer three basic questions:
- What can we deliver in this Sprint?
- How will we get the work done?
- Who will do that?
Sprint Planning meeting does not have to be boring and a waste of time. If you conduct it correctly, it can be the most stimulating time in your race. The purpose of this meeting is to leave each team member with an idea of the things they will accomplish.
How Can You Do This Efficiently?
Let’s break it into simple steps.
Step 1: Preparation
A great start leads to great results.
The PO’s Job: The Product Owner (PO) is the key player and initiator of this meeting. They must come with a prepared Product Backlog. The most important items at the top should be clear, detailed, and prioritized. It is like a menu of the team for the Sprint.
The Team’s Job: So, PO is involved in preparing this list. The team’s crucial job is to be already familiar with that backlog from previous refinement sessions.
Step 2: Set the Stage (First 15 Minutes)
Everyone is getting ready. Begin with the review goal.
Review the Goal: The Product Owner is the responsible person for kicking off the presentation of the Sprint goal. This is a short, clear statement of what the team aims to achieve by the end of the Sprint. For example, “Allow users to reset their password securely without needing to contact customer support.” This provides the team with a shared purpose, not just a list of tasks.
Review the Backlog: The PO then takes the team through the high-priority items from the backlog that could help achieve that goal.
Step 3: Choose the work (The “What”)
The team can set a realistic commitment to delivering.
Discuss and Ask Questions: The team reviews each potential backlog item. Developers and Testers may ask these questions:
- “What does ‘done’ look like for this?”
- “Are there any hidden challenges?”
Select the items: Collectively, the team decides how many of these top items they can realistically finish in the Sprint. This is a team decision, not a command from the PO or Scrum Master. The selected items move from the Product Backlog to the Sprint Backlog.
Step 4: Divide and Allocate it (The “How”)
Put plans into action. For each backlog item selected, the team needs to create a game plan.
Create a Task List: Breakdown each backlog item (usually a “User Story”) into small, specific, and actionable tasks. Let’s consider an example: the “password reset” story task list will contain:
- Create UI mockups for reset flow,
- Develop a backend API for password validation,
- Implement email notification service,
- Write integration tests for the complete workflow.
Estimate Effort: Most of the teams find this useful to calculate the time or complexity of these tasks. Make sure the workload is realistic and well-distributed among team members.
Step 5: Finalize The Plan
Before finishing, do you do a quick check?
Review the Plan: Take a final look at the Sprint Backlog.
- Does everyone understand the tasks?
- Does the plan look achievable?
Confirm Commitment: The scrum master responsible is getting the final confirmation from each team member that orally agrees to the Sprint Goal and the established plan. The powerful question Does everyone feel confident in our plan?” brings true team engagement.
Some Useful Tips For Success:
Follow these valuable, simple tips to become successful:
- Time-box it: A two-week Sprint usually requires a maximum of a two-hour planning meeting. Engage it focused.
- Invest in the Right Skills: Gain the required skills through the CSM certification course, which brings you a deep understanding of the Scrum practices and essential skills to run successful Sprint planning meetings.
- Ensure Everyone’s Participation: Not only for POs and Scrum Masters. This is for all team members. Encourage them to participate and make them involved in discussions.
- Deploy a Scrum Master to Facilitate: The Scrum Master should facilitate the entire meeting to avoid conflict in the discussions. Ensure the meeting is on track, remove roadblocks, and encourage team members to be cross-functional.
Final Thoughts:
Teams following an effective Sprint Planning meeting are achieving 80 to 90% of their goal as planned. Teams that have “successful” meetings are much more likely to complete their work on time and feel proud about what they have built. It sets an example for everyone to follow for a smooth and successful Sprint.
BUSINESS
ExcellenceGet.net/: Empowering Businesses to Excel

Success in today’s competitive business world requires more than just determination—it demands excellence. That’s where ExcellenceGet.net/ comes in. Designed for startups, digital marketers, and entrepreneurs, the platform delivers expert insights on business excellence, leadership strategies, and management solutions. Whether you’re looking to master the art of leadership or refine your digital strategies, ExcellenceGet.net/ provides the tools and resources to help your business thrive.
Why Excellence Matters in Business
Excellence isn’t just a buzzword—it’s the foundation upon which thriving businesses are built. It drives innovation, fosters creativity, and creates trust with customers and stakeholders. Committing to excellence early ensures a stronger, more sustainable foundation for startups and entrepreneurs. For digital marketers, prioritizing excellence sharpens campaigns and ensures higher ROI. At every stage, excellence differentiates successful businesses from their competitors.
Key benefits of pursuing business excellence include:
- Improving operational efficiency
- Building a strong, trustworthy brand
- Increasing customer satisfaction
- Driving consistent business growth
Excellence isn’t an option—it’s a necessity.
How ExcellenceGet.net Supports Your Business Growth
ExcellenceGet.net is a one-stop platform specifically designed to help businesses reach their full potential. With its comprehensive library of expert-curated content, the platform empowers you to face challenges, innovate, and grow with confidence.
Features and Tools Offered by ExcellenceGet.net
- Business Excellence Articles
- Leadership Resources
- Case Studies
- Exclusive Community for Entrepreneurs and Marketers
- Keyword Research
Use tools like Google Keyword Planner to identify terms that your target audience is searching for. Focus on long-tail keywords for better targeting.
- Content Optimization
Publish high-quality content that addresses customer pain points. Platforms like ExcellenceGet.net provide valuable insights into how to create impactful content.
- Technical SEO
Ensure your website is mobile-friendly, fast, and free of crawling issues. Tools such as SEMrush can help with diagnostics.
- Backlink Building
Focus on acquiring backlinks from industry leaders and related websites to boost your authority.
ExcellenceGet.net’s resources even include tips on SEO content creation tailored for startups!
Enhancing Digital Marketing Strategies with ExcellenceGet
Digital marketers require tools and insights that enable strategic, creative, and efficient execution. ExcellenceGet.net offers just that—actionable advice and proven tactics to enhance marketing strategies and boost campaign performance.
Ways digital marketers can benefit from ExcellenceGet:
- Learn how to craft high-impact campaigns that align with brand values.
- Discover tools to analyze campaign performance and refine targeting.
- Gain insights into creating share-worthy content tailored to your audience.
- Understand how to use customer feedback for continuous improvement.
With ExcellenceGet.net as your guide, you can elevate your digital marketing efforts and ensure excellence at every stage of a campaign.
The Future of Excellence in Business
The business of tomorrow will look vastly different from what it is today. Excellence will no longer be a differentiator—it will be the standard. Platforms like ExcellenceGet are at the forefront of this change, empowering businesses to adapt, innovate, and excel.
Here’s what the future of business excellence looks like:
- AI-Driven Decision Making
AI and machine learning will play an integral role in helping businesses implement smarter, more efficient strategies.
- Sustainability and Ethics
Companies pursuing excellence will increasingly prioritize ethical practices and sustainability.
- Personalized Leadership Approaches
Businesses will shift toward more personalized approaches in leadership and team management.
ExcellenceGet.net is dedicated to helping you and your business stay ahead in this rapidly evolving landscape.
Achieve Business Excellence with ExcellenceGet.net
Excellence isn’t achieved overnight—it’s the result of deliberate effort, expert guidance, and continual improvement. For startups, digital marketers, and entrepreneurs alike, ExcellenceGet.net offers the resources, tools, and community needed to thrive.
Explore ExcellenceGet.net today and take your business to the next level!
[Visit ExcellenceGet.net/ and Start Your Journey]
Conclusion
In this fast-paced and ever-evolving business landscape, achieving excellence requires a proactive approach, continuous learning, and the right resources. At ExcellenceGet.net/, we are committed to helping you and your business thrive, providing the tools, resources, and a supportive community needed to stay ahead. Embrace AI-driven decision-making, prioritize sustainability and ethics, and adopt personalized leadership approaches to unlock the full potential of your business. Start your journey towards business excellence today and explore everything ExcellenceGet.net/ has to offer. Together, let’s take your business to the next level!
[Visit ExcellenceGet.net and Start Your Journey]
FAQs
Q: What kind of resources does ExcellenceGet.net offer?
A: ExcellenceGet.net offers a wide range of resources to help businesses thrive. From articles and guides on various business topics to templates, frameworks, and tools, we provide comprehensive support to help you navigate the challenges and opportunities of the business world.
Q: Is ExcellenceGet.net/ only for startups?
A: No, ExcellenceGet.net/ is designed to support startups, digital marketers, and entrepreneurs of all levels. Whether you’re just starting or looking to take your established business to new heights, you will find valuable insights, resources, and a supportive community at ExcellenceGet.net/.
Q: How can I stay updated with the latest trends and insights?
A: ExcellenceGet.net/ is committed to keeping you informed and up-to-date. We regularly publish articles, case studies, and research papers on the latest trends, strategies, and best practices in business. Additionally, our community forums provide a platform for discussion and knowledge sharing among industry experts and fellow entrepreneurs.
Q: Can ExcellenceGet.net/ help with personalized leadership approaches?
A: Absolutely! At ExcellenceGet.net/, we understand the importance of leadership in driving business success. We offer resources and guidance on developing personalized leadership styles that align with your values and business goals. We aim to help you unlock your leadership potential and inspire your team to achieve excellence.
Q: How can I get involved with the ExcellenceGet.net/ community?
A: Joining the ExcellenceGet.net community is easy! Simply create an account on our website to gain access to our resources, forums, and networking opportunities. Engage with fellow entrepreneurs, share your experiences, and learn from others who are on a similar journey to business excellence.
Have more questions? Don’t hesitate to reach out to our support team. We’re here to assist you every step of the way on your path to business excellence.
-
 TECHNOLOGY1 year ago
TECHNOLOGY1 year agoM6 auc 4s0101 Chip: Revolutionizing Automotive Electronics
-

 NOODLEMAGAZINE1 year ago
NOODLEMAGAZINE1 year agoNoodleMagazine: Bridging Cultures
-

 ENTERTAINMENT1 year ago
ENTERTAINMENT1 year agoNoodleMagazine: Stirring Up Culinary Creativity
-

 HEALTH & FITNESS2 years ago
HEALTH & FITNESS2 years agoHow NoodleMagazine is Shaping Modern Asian Cuisine Trends
-

 NOODLEMAGAZINE1 year ago
NOODLEMAGAZINE1 year agoDiscover the NoodleMagazine
-

 HEALTH & FITNESS1 year ago
HEALTH & FITNESS1 year agoHow NoodleMagazine Inspires Home Cooks
-

 BUSINESS1 year ago
BUSINESS1 year agoAjay Attaho: Revolutionizing Freelancing, Tech, and Startups
-

 HEALTH & FITNESS2 years ago
HEALTH & FITNESS2 years agoThe Top 5 Foam Play Mats Reviewed!







































